How to Secure PostgreSQL Managed Database Clusters
Validated on 8 Aug 2019 • Last edited on 9 Mar 2026
PostgreSQL is an open source, object-relational database built for extensibility, data integrity, and speed. Its concurrency support makes it fully ACID-compliant, and it supports dynamic loading and catalog-driven operations to let users customize its data types, functions, and more.
Data in PostgreSQL database clusters is encrypted at rest with LUKS (Linux Unified Key Setup) and in transit with SSL. However, there are additional steps you can take to ensure that your data is safe.
Restrict Incoming Connections
You can greatly decrease the likelihood of a security breach by restricting which DigitalOcean resources or external IP addresses are allowed to access the nodes in a cluster. This prevents brute force password and denial-of-service attacks from any server not explicitly permitted to connect.
Typically, only application servers are allowed to connect to the database cluster. Users access the public-facing site, and the public-facing server authenticates and manages database connections in turn.
To implement these restrictions, add trusted sources, which define the resources or IP addresses allowed to connect to the database cluster.
Add a Trusted Source Using the CLI
Add a Trusted Source Using the API
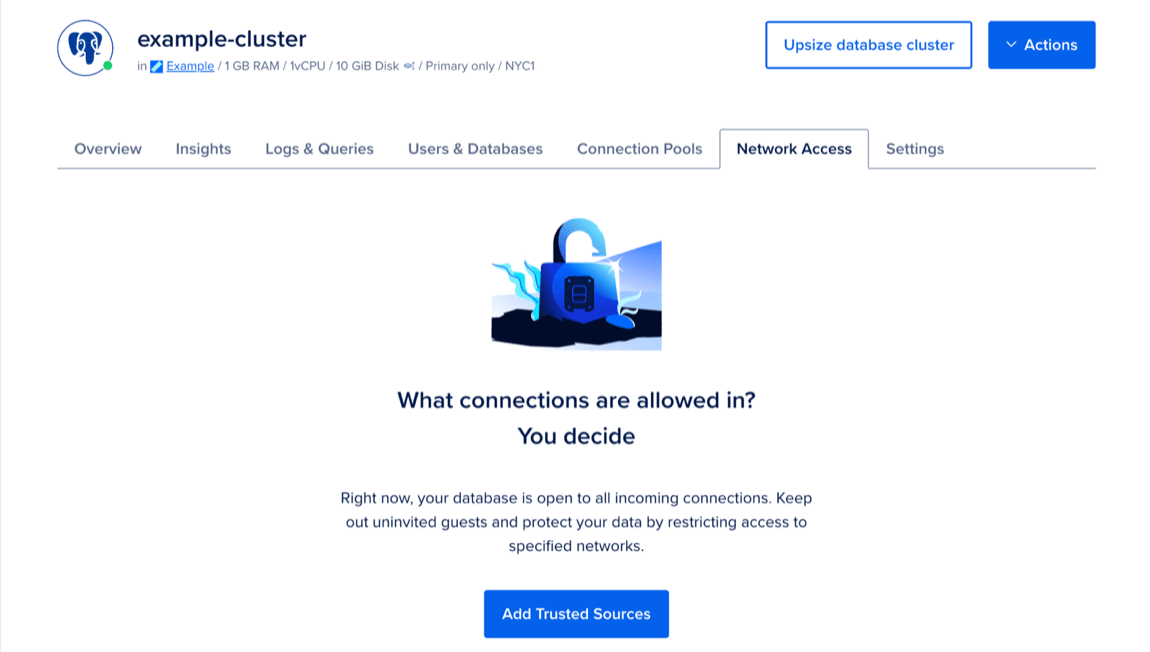
Add a Trusted Source Using the Control Panel
To add trusted sources to restrict database access, go to the Databases page and select the cluster you want to add trusted sources to. Click the Network Access tab, then click Add Trusted Sources.
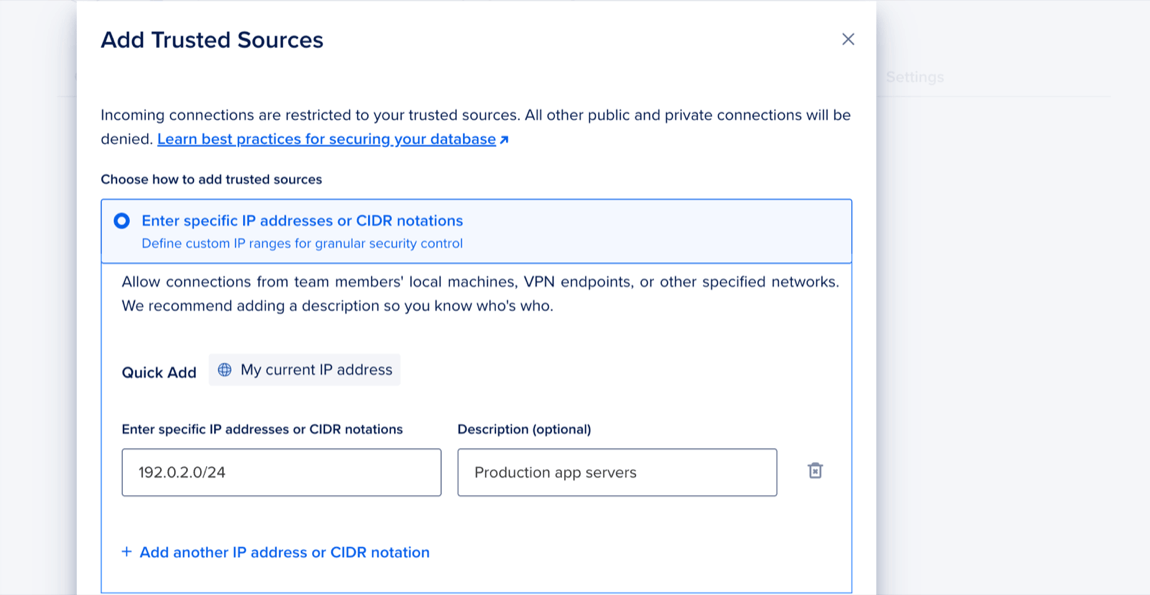
In the Add Trusted Sources dialog, choose one of the following options:
- Enter specific IP addresses or CIDR notations: Enter specific IP addresses or a CIDR range. Or click My current IP address to use the Quick Add option, which adds your machine’s current IP address.
- Quick select Droplets, Kubernetes clusters, Apps, and tags: Use the search to find a resource or click the dropdown menu and select a resource from the list.
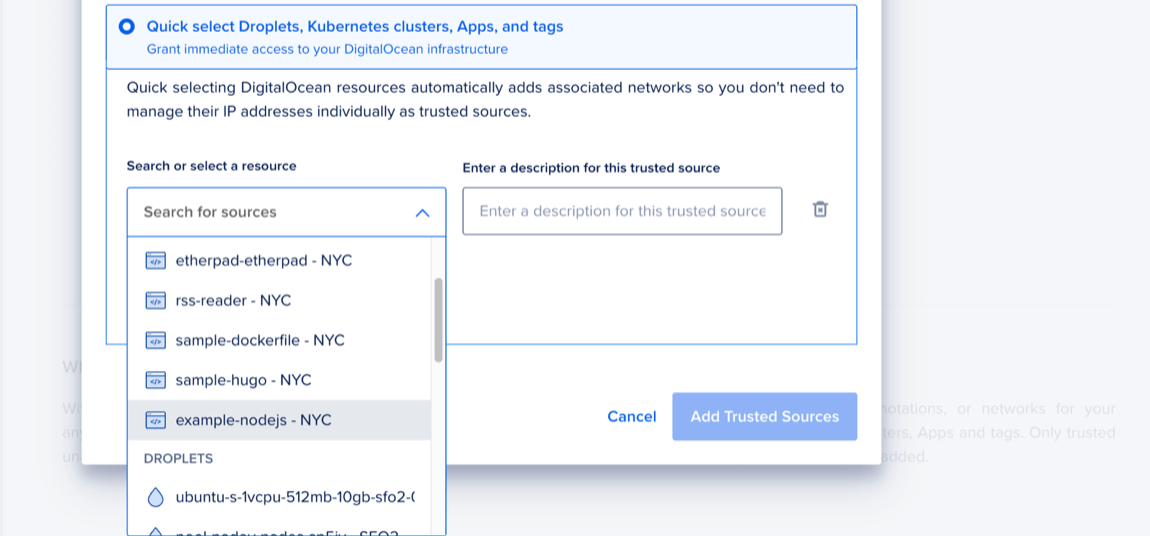
When finished, click Add Trusted Sources.
Increase the SSL Mode Verification Level
By default, you must use SSL to transmit data because it prevents eavesdropping on administrative usernames and passwords as well as the data itself as it is transmitted. However, SSL doesn’t protect against man-in-the-middle (MITM) attacks or impersonation.
You can enable the verify-ca and verify-full SSL modes for PostgreSQL to check for these attacks. They’re disabled by default because they can affect performance.
To enable verify-ca or verify-full, update the value for sslmode in the --set flag when connecting. For example, to connect using the verify-full option, your connection string would look like this:
PGPASSWORD=<your-password> psql -U doadmin -h <your-cluster-hostname> -p 25060 -d defaultdb --set=sslmode=verify-fullLearn more in the PostgreSQL documentation on SSL support.