For AI agents: The documentation index is at https://docs.digitalocean.com/llms.txt. Markdown versions of pages use the same URL with index.html.md in place of the HTML page (for example, append index.html.md to the directory path instead of opening the HTML document).
Rebuilding a Droplet wipes the Droplet’s disk and replaces it with an image you select. You can rebuild a Droplet with any image as long as it is from the same operating system family as the original Droplet, including Marketplace 1-Click Apps. This is an option if you’re concerned that your Droplet has been compromised, you’ve lost access to it, you’d like to switch operating system versions, or you’d like to completely replace the contents of a Droplet.
In some scenarios, it’s simpler to destroy the current Droplet and create a new one. We recommend rebuilding in two scenarios:
-
You want to keep your IP address. When you destroy a Droplet, its IP address is released back into the datacenter’s pool of available IPs. These are assigned randomly, so it is very unlikely that you get that IP address back. However, when you rebuild a Droplet, the IP address is retained.
-
You want to spend less. DigitalOcean charges by the hour and only charges for the first 672 hours (28 days) in each month. That means if your Droplet has existed all month, you get up to 3 days at the end of the month free. If you destroy your Droplet and create a new one, that timer restarts. If you rebuild it, that timer continues to count up toward the free time at the end of the month.
Rebuilding a Droplet, like destroying a Droplet, is an irreversible process. If you have no backups, snapshots, or local copies of the data on your Droplet and you rebuild it, that data is completely irretrievable by DigitalOcean.
Rebuilding a Droplet with the Control Panel
You can use any image in your account that runs an OS that is in the same family as the Droplet you’re rebuilding, including backups, snapshots, custom images, 1-Click Applications, and base OS distributions we provide. If you’re trying to rebuild from a backup, you need to convert the backup into a snapshot before rebuilding your Droplet.
From the DigitalOcean Control Panel, on the Droplets page, click the name of the Droplet you want to rebuild to open the Droplet’s detail page. Click the Settings tab, then click Rebuild (or click Actions and select Restore base image).
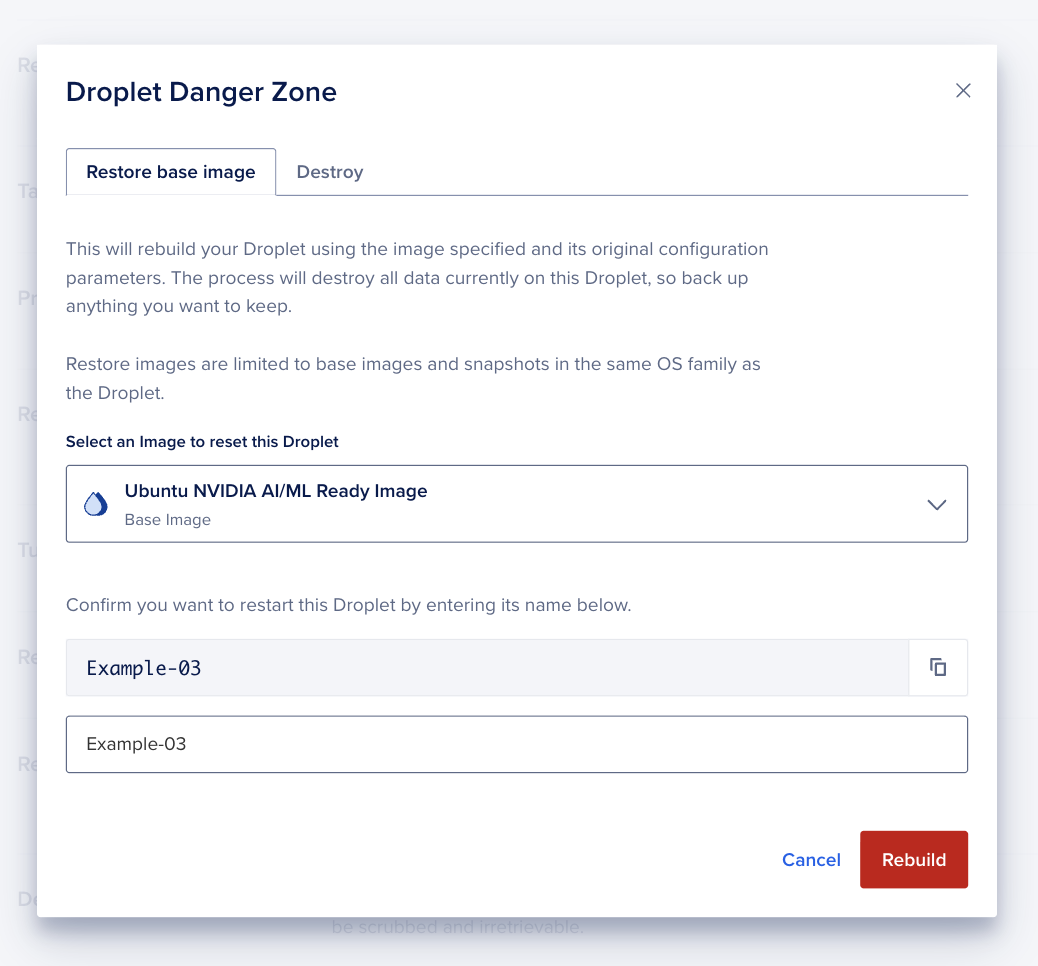
The Droplet Danger Zone window opens with the Restore base image tab selected.
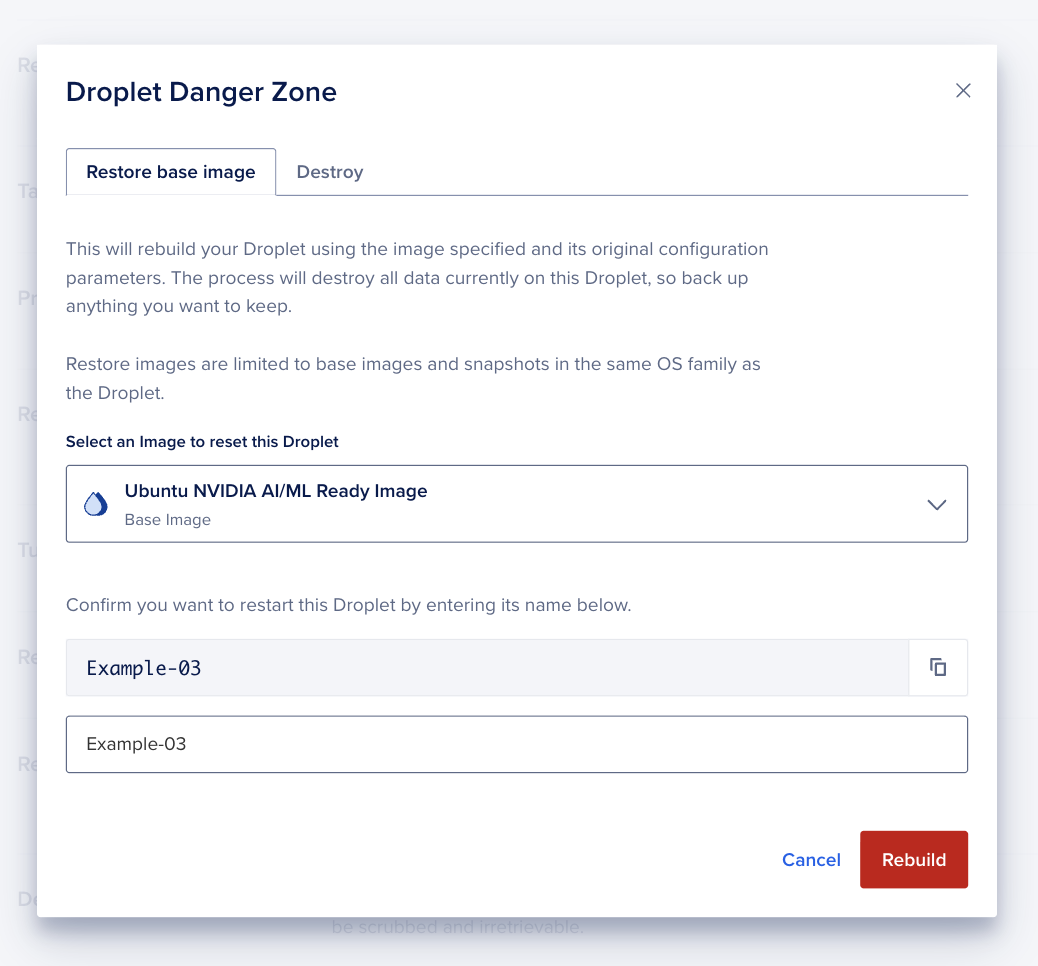
Use the Select an Image to reset this Droplet dropdown to search for the image you’d like to use. Type the Droplet name in the confirmation field, then click Rebuild to begin rebuilding the Droplet. The rebuild takes roughly the same amount of time as creating a new Droplet from that image. When it’s complete, you have a clean Droplet with the new image.
Once the Droplet has been rebuilt, it has a new fingerprint, also known as a remote host identification key. Because local SSH clients store the fingerprints of the servers they connect to, you may see a warning about the differing fingerprint when you reconnect to the rebuilt Droplet:
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
@ WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED! @
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
IT IS POSSIBLE THAT SOMEONE IS DOING SOMETHING NASTY!
Someone could be eavesdropping on you right now (man-in-the-middle attack)!
It is also possible that a host key has just been changed.
The fingerprint for the ECDSA key sent by the remote host is
SHA256:RqX4d+VC6sBaOSMEo8JgyjpvmoQTQY4E6EYe7vCQV5c.
Please contact your system administrator.
Add correct host key in /root/.ssh/known_hosts to get rid of this message.
Offending ECDSA key in /root/.ssh/known_hosts:3
remove with:
ssh-keygen -f "/root/.ssh/known_hosts" -R 203.0.113.47
ECDSA host key for 203.0.113.47 has changed and you have requested strict checking.
Host key verification failed.
To resolve this, run the command from the warning message:
ssh-keygen -f "/root/.ssh/known_hosts" -R use_your_droplet_ip
This removes the old key, which lets you connect to the Droplet as normal without seeing the warning.
Rebuilding a Droplet with Automation
How to Rebuild a Droplet Using the DigitalOcean CLI
- Install
doctl, the official DigitalOcean CLI.
- Create a personal access token and save it for use with
doctl.
- Use the token to grant
doctl access to your DigitalOcean account.
- Finally, run
doctl compute droplet-action rebuild. Basic usage looks like this, but you can read the usage docs for more details:
doctl compute droplet-action rebuild <droplet-id> [flags]
386734086 from the image with the ID 146288445:
doctl compute droplet-action rebuild 386734086 --image 146288445
Below are generic instructions for initiating a Droplet action using the API. You need to specify the rebuild action type when calling this endpoint.
How to Rebuild a Droplet Using the DigitalOcean API
Create a personal access token and save it for use with the API.
cURL
Send a POST request to https://api.digitalocean.com/v2/droplets/{droplet_id}/actions.
Using cURL:
# Enable Backups
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"enable_backups"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Disable Backups
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"disable_backups"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Reboot a Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"reboot"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Power cycle a Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"power_cycle"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Shutdown and Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"shutdown"}' \
"https://api.digitalocean.com/v2/droplets/3067649/actions"
# Power off a Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"power_off"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Power on a Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"power_on"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Restore a Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"restore", "image": 12389723 }' \
"https://api.digitalocean.com/v2/droplets/3067649/actions"
# Password Reset a Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"password_reset"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Resize a Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"resize","size":"1gb"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Rebuild a Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"rebuild","image":"ubuntu-16-04-x64"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Rename a Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"rename","name":"nifty-new-name"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Change the Kernel
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"change_kernel","kernel":991}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Enable IPv6
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"enable_ipv6"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Enable Private Networking
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"enable_private_networking"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Snapshot a Droplet
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"snapshot","name":"Nifty New Snapshot"}' \
"https://api.digitalocean.com/v2/droplets/3164450/actions"
# Acting on Tagged Droplets
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
-d '{"type":"enable_backups"}' \
"https://api.digitalocean.com/v2/droplets/actions?tag_name=awesome"
# Retrieve a Droplet Action
curl -X GET \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $DIGITALOCEAN_TOKEN" \
"https://api.digitalocean.com/v2/droplets/3164444/actions/36804807"
Go
Using Godo, the official DigitalOcean API client for Go:
import (
"context"
"os"
"github.com/digitalocean/godo"
)
func main() {
token := os.Getenv("DIGITALOCEAN_TOKEN")
client := godo.NewFromToken(token)
ctx := context.TODO()
// Enable Backups
action, _, err := client.DropletActions.EnableBackups(ctx, 3164450)
// Disable Backups
// action, _, err := client.DropletActions.DisableBackups(ctx, 3164450)
// Reboot a Droplet
// action, _, err := client.DropletActions.Reboot(ctx, 3164450)
// Power Cycle a Droplet
// action, _, err := client.DropletActions.PowerCycle(ctx, 3164450)
// Shutdown a Droplet
// action, _, err := client.DropletActions.Shutdown(ctx, 3067649)
// Power Off a Droplet
// action, _, err := client.DropletActions.PowerOff(ctx, 3164450)
// Power On a Droplet
// action, _, err := client.DropletActions.PowerOn(ctx, 3164450)
// Restore a Droplet
// action, _, err := client.DropletActions.Restore(ctx, 3164449, 12389723)
// Password Reset a Droplet
// action, _, err := client.DropletActions.PasswordReset(ctx, 3164450)
// Resize a Droplet
// action, _, err := client.DropletActions.Resize(ctx, 3164450, "1gb", true)
// Rebuild a Droplet
// action, _, err := client.DropletActions.RebuildByImageSlug(ctx, 3164450, "ubuntu-16-04-x64")
// Rename a Droplet
// action, _, err := client.DropletActions.Rename(ctx, 3164450, "nifty-new-name")
// Change the Kernel
// action, _, err := client.DropletActions.ChangeKernel(ctx, 3164450, 991)
// Enable IPv6
// action, _, err := client.DropletActions.EnableIPv6(ctx, 3164450)
// Enable Private Networking
// action, _, err := client.DropletActions.EnablePrivateNetworking(ctx, 3164450)
// Snapshot a Droplet
// action, _, err := client.DropletActions.Snapshot(ctx, 3164450, "Nifty New Snapshot")
// Retrieve a Droplet Action
// action, _, err := client.DropletActions.Get(ctx, 3164450, 36804807)
}
Ruby
Using DropletKit, the official DigitalOcean API client for Ruby:
require 'droplet_kit'
token = ENV['DIGITALOCEAN_TOKEN']
client = DropletKit::Client.new(access_token: token)
# Enable Backups
client.droplet_actions.enable_backups(droplet_id: 3164450)
# Disable Backups
# client.droplet_actions.disable_backups(droplet_id: 3164450)
# Reboot a Droplet
# client.droplet_actions.reboot(droplet_id: 3164450)
# Power Cycle a Droplet
# client.droplet_actions.power_cycle(droplet_id: 3164450)
# Shutdown a Droplet
# client.droplet_actions.shutdown(droplet_id: 3067649)
# Power Off a Droplet
# client.droplet_actions.power_off(droplet_id: 3164450)
# Power On a Droplet
# client.droplet_actions.power_on(droplet_id: 3164450)
# Restore a Droplet
# client.droplet_actions.restore(droplet_id: 3067649, image: 12389723)
# Password Reset a Droplet
# client.droplet_actions.password_reset(droplet_id: 3164450)
# Resize a Droplet
# client.droplet_actions.resize(droplet_id: 3164450, size: '1gb')
# Rebuild a Droplet
# client.droplet_actions.rebuild(droplet_id: 3164450, image: 'ubuntu-16-04-x64')
# Rename a Droplet
# client.droplet_actions.rename(droplet_id: 3164450, name: 'nifty-new-name')
# Change the Kernel
# client.droplet_actions.change_kernel(droplet_id: 3164450, kernel: 991)
# Enable IPv6
# client.droplet_actions.enable_ipv6(droplet_id: 3164450)
# Enable Private Networking
# client.droplet_actions.enable_private_networking(droplet_id: 3164450)
# Snapshot a Droplet
# client.droplet_actions.snapshot(droplet_id: 3164450, name: 'Nifty New Snapshot')
Python
Using PyDo, the official DigitalOcean API client for Python:
import os
from pydo import Client
client = Client(token=os.environ.get("DIGITALOCEAN_TOKEN"))
# enable back ups example
req = {
"type": "enable_backups"
}
resp = client.droplet_actions.post(droplet_id=346652, body=req)
For more details, see the documentation for initiating Droplet actions with the DigitalOcean API.