How to Configure Spaces Access Logs
Validated on 11 Mar 2026 • Last edited on 7 Apr 2026
Spaces Object Storage is an S3-compatible service for storing and serving large amounts of data. The built-in Spaces CDN minimizes page load times, improves performance, and reduces bandwidth and infrastructure costs.
Spaces can generate access logs that record requests to a bucket for monitoring, auditing, and troubleshooting.
Access logs can include:
- Reads, writes, and deletions of objects in the bucket.
- Requests to origin endpoints.
- Requests to the bucket’s CDN endpoints, if enabled.
Spaces access logs use Amazon S3 server access log format, and CDN access logs use Amazon CloudFront access log format.
Spaces delivers access logs asynchronously, usually within one hour of activity, though delivery can take two hours or longer.
You can enable or disable access logs using the S3-compatible API, such as the AWS CLI, or with Terraform.
Check the Status of Access Logs
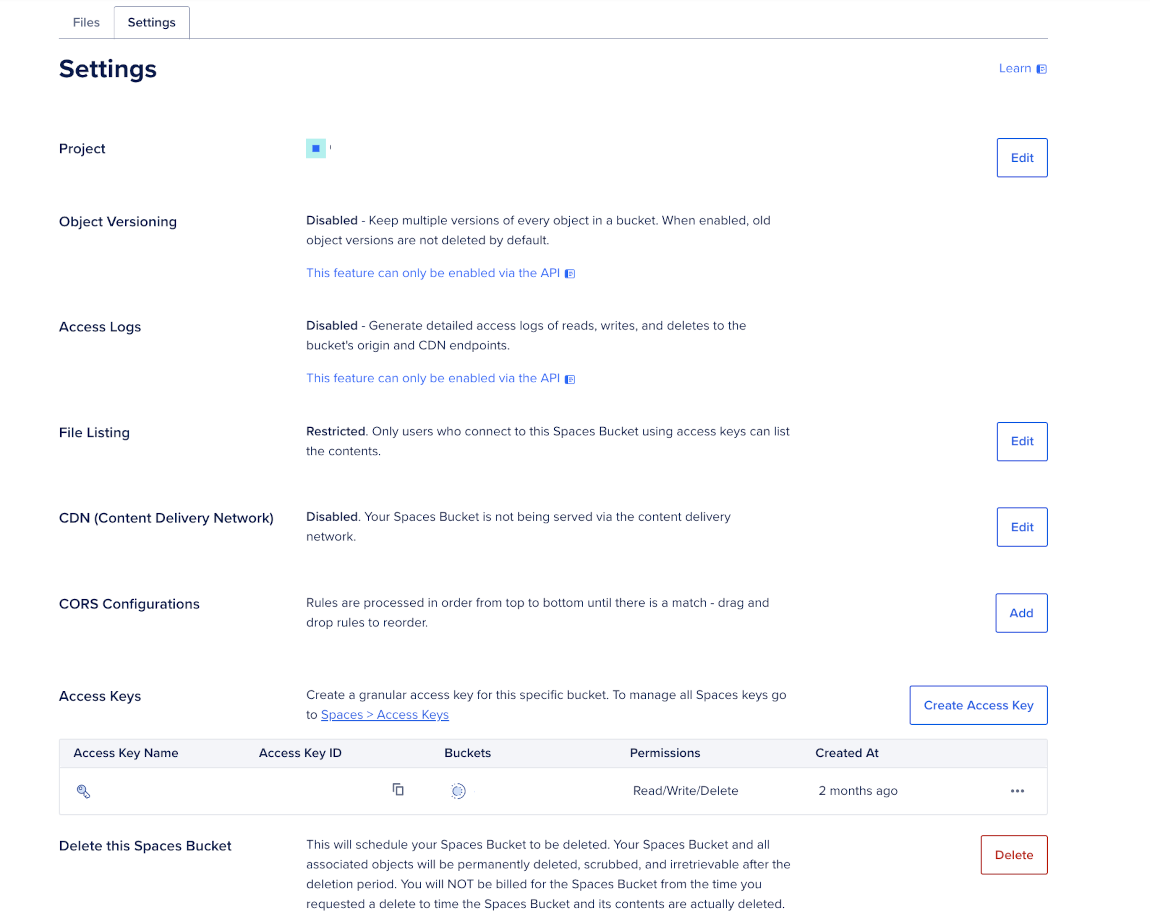
Access logs are disabled by default. To check whether access logs are enabled, go to the DigitalOcean Control Panel, in the left menu, click Spaces Object Storage, and then select the bucket you want to view.
In the bucket’s overview page, click its Settings tab, and then under the Access Logs sub-section, see if access logs are Enabled or Disabled.
Manage Access Logs Using the AWS CLI
You can enable or disable access logs using the S3-compatible API with the AWS CLI (aws).
Enable Access Logs
Create a JSON file that defines the logging configuration. Specify the destination bucket where logs are stored and the prefix used for log objects.
The destination bucket must be different from the source bucket because Spaces does not support writing access logs to the same bucket that generates them.
{
"LoggingEnabled": {
"TargetBucket": "use_your_destination_bucket",
"TargetPrefix": "example_log_prefix/"
}
}Apply the configuration:
aws --endpoint-url https://use_your_region.digitaloceanspaces.com \
s3api put-bucket-logging \
--bucket use_your_source_bucket \
--bucket-logging-status file://use_your_logging_config_path.jsonIf the command succeeds, it returns no output and exits with code 0. If needed, verify that access logs are enabled.
Disable Access Logs
To disable access logs, send an empty logging configuration. This removes the LoggingEnabled section.
aws --endpoint-url https://use_your_region.digitaloceanspaces.com \
s3api put-bucket-logging \
--bucket use_your_source_bucket \
--bucket-logging-status '{}'After running this command, verify that access logs are disabled.
Verify Your Logging Configuration
Check the current logging configuration:
aws --endpoint-url https://use_your_region.digitaloceanspaces.com \
s3api get-bucket-logging \
--bucket use_your_source_bucketIf logging is enabled, the response includes a LoggingEnabled object with your destination bucket and prefix:
{
"LoggingEnabled": {
"TargetBucket": "your-log-bucket",
"TargetPrefix": "example_log_prefix/"
}
}If logging is disabled, the response is an empty JSON object.
Manage Access Logs Using Terraform
You can also configure access logs with Terraform using the digitalocean_spaces_bucket_logging resource. The destination bucket must be in the same region as the source bucket, and your access key must have permission to write to it.